Resolve SQL Server Database Stuck in Suspect Mode Problem Easily
Summary: Many times SQL Database administrators encounters SQL server database stuck in suspect mode issue. Due to inaccessibility of the database objects, all the DBA’s try to bring the database online as soon as possible because. So this problem tackling blog will discuss the steps by step process to resolve SQL Database Marked as Suspect issue.Suspect Mode in SQL Server database means the recovery process has started but not finished successfully. The user will not be able to connect to the database nor the user can recover it. All the database objects will be inaccessible. This issue will clearly reflect the risk of data loss.
“Urgent Please! When I woke up in the morning and found my company SQL database is marked as suspect. I do not have the backup and I want to bring the database online as soon as possible. Please help me to resolve this problem.”
Why SQL Server Database Stuck in Suspect Mode? Know the Reasons
Before Proceeding to solution part we have to discuss various causes for this problem. Here are the reason responsible for SQL Database Marked as Suspect mode.- Improper or forcefully shutdown of the SQL Server.
- In case if the system failed to open the device where the data or the log file resides.
- Due to lack of disk space may be the reason for this problem.
- In case of SQL Server crash issue, or if the database files are used by the third party backup software.
- If SQL database cannot complete roll forward or rollback operation.
Solve SQL Server Database Stuck in Suspect Mode Problem Manually
Follow the steps below to resolve this problem manually1. First the user has to Switch the database to Emergency Mode. For this Launch the SQL Server Management studio and then connect to your database. After that select the New Query option.
Execute This Command
EXEC sp_resetstatus 'your database name';
ALTER DATABASE db_name SET EMERGENCY
This will turn of the suspect flag and switch off to Emergency Mode.
2. Now Perform the Consistency check
DBCC CHECKDB (‘Your databasename’)
3. Bring the database into Single User Mode
ALTER DATABASE your database name SET SINGLE_USER WITH ROLLBACK IMMEDIATE
4. Backup your database because the next command can cause data loss situation.
5. Now Execute the following command
DBCC CHECKDB ('Your database name', REPAIR_ALLOW_DATA_LOSS)
6. After this Change the database into Multi User Mode.
ALTER DATABASE database_name SET MULTI_USER
Finally the user to refresh the SQL serve database and check the connectivity issues.
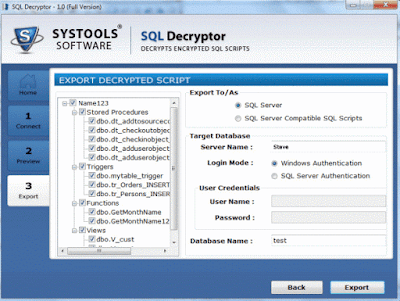
Note: The user can try the above steps to resolve SQL server database stuck in suspect mode. But in this problem there is a high risk of data loss. So in that case the user can try SQL database recovery tool to resolve this issue. SQL database Recovery Tool is capable to repair the database from suspect mode. The user can easily Recover SQL Database objects such as SQL tables, stored procedure, functions, triggers, indexes. Also this application shows the preview of deleted SQL table records in red color.